Hacking home Stock Vectors & Vector Art
 hacking home safe securities, robbery. Comic cartoon pop art retro vector illustration drawing Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/hacking-home-safe-securities-robbery-comic-cartoon-pop-art-retro-vector-illustration-drawing-image264504688.html
hacking home safe securities, robbery. Comic cartoon pop art retro vector illustration drawing Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/hacking-home-safe-securities-robbery-comic-cartoon-pop-art-retro-vector-illustration-drawing-image264504688.htmlRFWA96C0–hacking home safe securities, robbery. Comic cartoon pop art retro vector illustration drawing
 Thief and criminal. Home robbery, theft burglary cartoon. Burglar, cybercrime or hackers, utter database hacking and robbers vector characters Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/thief-and-criminal-home-robbery-theft-burglary-cartoon-burglar-cybercrime-or-hackers-utter-database-hacking-and-robbers-vector-characters-image449658323.html
Thief and criminal. Home robbery, theft burglary cartoon. Burglar, cybercrime or hackers, utter database hacking and robbers vector characters Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/thief-and-criminal-home-robbery-theft-burglary-cartoon-burglar-cybercrime-or-hackers-utter-database-hacking-and-robbers-vector-characters-image449658323.htmlRF2H3FKNR–Thief and criminal. Home robbery, theft burglary cartoon. Burglar, cybercrime or hackers, utter database hacking and robbers vector characters
 IOT cybersecurity spider concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/iot-cybersecurity-spider-concept-personal-data-safety-internet-of-things-smart-home-cyber-attack-hacker-attack-danger-firewall-innovation-system-image240575385.html
IOT cybersecurity spider concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/iot-cybersecurity-spider-concept-personal-data-safety-internet-of-things-smart-home-cyber-attack-hacker-attack-danger-firewall-innovation-system-image240575385.htmlRFRYB4A1–IOT cybersecurity spider concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system
 spyware monitors a woman messages on a smartphone Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/spyware-monitors-a-woman-messages-on-a-smartphone-image350576387.html
spyware monitors a woman messages on a smartphone Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/spyware-monitors-a-woman-messages-on-a-smartphone-image350576387.htmlRF2BAA3N7–spyware monitors a woman messages on a smartphone
 IOT cybersecurity spider concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/iot-cybersecurity-spider-concept-personal-data-safety-internet-of-things-smart-home-cyber-attack-hacker-attack-danger-firewall-innovation-system-image240435523.html
IOT cybersecurity spider concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/iot-cybersecurity-spider-concept-personal-data-safety-internet-of-things-smart-home-cyber-attack-hacker-attack-danger-firewall-innovation-system-image240435523.htmlRFRY4NXY–IOT cybersecurity spider concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system
 Software piracy, the hacker captain Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-software-piracy-the-hacker-captain-119737812.html
Software piracy, the hacker captain Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-software-piracy-the-hacker-captain-119737812.htmlRFGXPEPC–Software piracy, the hacker captain
 IOT cyber security padlock concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/iot-cyber-security-padlock-concept-personal-data-safety-internet-of-things-smart-home-cyber-attack-hacker-attack-danger-firewall-innovation-system-image240575370.html
IOT cyber security padlock concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/iot-cyber-security-padlock-concept-personal-data-safety-internet-of-things-smart-home-cyber-attack-hacker-attack-danger-firewall-innovation-system-image240575370.htmlRFRYB49E–IOT cyber security padlock concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system
 Burglar in the house isolated vector illustration EPS10 Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/burglar-in-the-house-isolated-vector-illustration-eps10-image216986820.html
Burglar in the house isolated vector illustration EPS10 Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/burglar-in-the-house-isolated-vector-illustration-eps10-image216986820.htmlRFPH0GW8–Burglar in the house isolated vector illustration EPS10
 Keyhole peeping the police state Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/keyhole-peeping-the-police-state-image366825862.html
Keyhole peeping the police state Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/keyhole-peeping-the-police-state-image366825862.htmlRF2C8PA3J–Keyhole peeping the police state
 Two saws isolated on white Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/two-saws-isolated-on-white-image555525633.html
Two saws isolated on white Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/two-saws-isolated-on-white-image555525633.htmlRF2R7PAH5–Two saws isolated on white
RF2HPK6FC–Skim Simple vector icon.
 Hacker attack, cybercrime flat vector illustration. Criminal in mask working with computer cartoon character. Thief stealing information, cyber safety breach, hacking process, cybersecurity concept Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/hacker-attack-cybercrime-flat-vector-illustration-criminal-in-mask-working-with-computer-cartoon-character-thief-stealing-information-cyber-safety-breach-hacking-process-cybersecurity-concept-image330413697.html
Hacker attack, cybercrime flat vector illustration. Criminal in mask working with computer cartoon character. Thief stealing information, cyber safety breach, hacking process, cybersecurity concept Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/hacker-attack-cybercrime-flat-vector-illustration-criminal-in-mask-working-with-computer-cartoon-character-thief-stealing-information-cyber-safety-breach-hacking-process-cybersecurity-concept-image330413697.htmlRF2A5FJ15–Hacker attack, cybercrime flat vector illustration. Criminal in mask working with computer cartoon character. Thief stealing information, cyber safety breach, hacking process, cybersecurity concept
RF2ARFK7Y–Scam types neon light icons set. Inheritance, home rental fraudulent scheme. Computer hacking. Employment scamming. Financial scamming. Illegal money
RF2B19EX2–Vpn icon set. Include creative elements , archiving, site security, home server, cloud storage hacking icons. Can be used for report, presentation
RF2HJGWJ6–filled internet security and icon set. contain flat wireless connection, phishing, hacker, hard disc, data protection, network funnel, scan, home netw
 Hacker is happy while hacking by desktop computer, vector cartoon Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-hacker-is-happy-while-hacking-by-desktop-computer-vector-cartoon-170740868.html
Hacker is happy while hacking by desktop computer, vector cartoon Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-hacker-is-happy-while-hacking-by-desktop-computer-vector-cartoon-170740868.htmlRFKWNWM4–Hacker is happy while hacking by desktop computer, vector cartoon
 flat cartoon character. cloud storage is protected from viruses and hacking to maintain servers and databases. database security use firewall and netw Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/flat-cartoon-character-cloud-storage-is-protected-from-viruses-and-hacking-to-maintain-servers-and-databases-database-security-use-firewall-and-netw-image368053942.html
flat cartoon character. cloud storage is protected from viruses and hacking to maintain servers and databases. database security use firewall and netw Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/flat-cartoon-character-cloud-storage-is-protected-from-viruses-and-hacking-to-maintain-servers-and-databases-database-security-use-firewall-and-netw-image368053942.htmlRF2CAP8FJ–flat cartoon character. cloud storage is protected from viruses and hacking to maintain servers and databases. database security use firewall and netw
RF2JB23AC–Security concept icons set with financial and home security symbols flat isolated vector illustration
RFT9F43C–Universal set for web and mobile. Hacker, photo, note, atm and other. Icons set with editable stroke
RF2XXM361–Surveillance icons collection is a vector illustration with editable stroke.
 Thief in black mask trying to force door flat vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/thief-in-black-mask-trying-to-force-door-flat-vector-illustration-image471643362.html
Thief in black mask trying to force door flat vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/thief-in-black-mask-trying-to-force-door-flat-vector-illustration-image471643362.htmlRF2JB95WP–Thief in black mask trying to force door flat vector illustration
RF2Y1H8JJ–Cyber security and artificial intelligence icons High-Quality Vector Icons Collection with Editable Stroke. Ideal for Professional and Creative Projec
 A programmer busy doing some coding Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/a-programmer-busy-doing-some-coding-image212667757.html
A programmer busy doing some coding Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/a-programmer-busy-doing-some-coding-image212667757.htmlRFP9YRW1–A programmer busy doing some coding
RF2PP8FNR–Holding company line icons collection. Cybersecurity, Encryption, Hacking, Firewall, Malware, Phishing, Cybercrime vector and linear illustration. VPN
 Software piracy, the hacker captain Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-software-piracy-the-hacker-captain-119539647.html
Software piracy, the hacker captain Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-software-piracy-the-hacker-captain-119539647.htmlRFGXDE13–Software piracy, the hacker captain
 IOT cyber security padlock concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/iot-cyber-security-padlock-concept-personal-data-safety-internet-of-things-smart-home-cyber-attack-hacker-attack-danger-firewall-innovation-system-image240575380.html
IOT cyber security padlock concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/iot-cyber-security-padlock-concept-personal-data-safety-internet-of-things-smart-home-cyber-attack-hacker-attack-danger-firewall-innovation-system-image240575380.htmlRFRYB49T–IOT cyber security padlock concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system
 cyber security concept Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/cyber-security-concept-image180912087.html
cyber security concept Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/cyber-security-concept-image180912087.htmlRFME975Y–cyber security concept
 IOT cyber security padlock concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/iot-cyber-security-padlock-concept-personal-data-safety-internet-of-things-smart-home-cyber-attack-hacker-attack-danger-firewall-innovation-system-image240254990.html
IOT cyber security padlock concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/iot-cyber-security-padlock-concept-personal-data-safety-internet-of-things-smart-home-cyber-attack-hacker-attack-danger-firewall-innovation-system-image240254990.htmlRFRXTFKA–IOT cyber security padlock concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system
RFPDB8FN–Construction, Renovation, and House Improvement Icons. Pictogram depicts workers working in different jobs and works at a construction sites.
 Robber open safe. Thief and money vault. Criminal vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/robber-open-safe-thief-and-money-vault-criminal-vector-illustration-image351656639.html
Robber open safe. Thief and money vault. Criminal vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/robber-open-safe-thief-and-money-vault-criminal-vector-illustration-image351656639.htmlRF2BC39HK–Robber open safe. Thief and money vault. Criminal vector illustration
 Thief in black mask trying to force door flat vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/thief-in-black-mask-trying-to-force-door-flat-vector-illustration-image474111034.html
Thief in black mask trying to force door flat vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/thief-in-black-mask-trying-to-force-door-flat-vector-illustration-image474111034.htmlRF2JF9HCX–Thief in black mask trying to force door flat vector illustration
RF2ARF9TC–Scam types neon light icons set. Malware. Investment, rental schemes. Phishing tricks. Cybercrime. Malicious internet activities. Financial fraud. Glo
RF2AMAJDA–Vpn icon set. Include creative elements , archiving, site security, home server, cloud storage hacking icons. Can be used for report, presentation
 man using smart phone controls smart home devices through a wireless connection. Secure smart home. control of smart home systems is available only fr Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/man-using-smart-phone-controls-smart-home-devices-through-a-wireless-connection-secure-smart-home-control-of-smart-home-systems-is-available-only-fr-image185064792.html
man using smart phone controls smart home devices through a wireless connection. Secure smart home. control of smart home systems is available only fr Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/man-using-smart-phone-controls-smart-home-devices-through-a-wireless-connection-secure-smart-home-control-of-smart-home-systems-is-available-only-fr-image185064792.htmlRFMN2C0T–man using smart phone controls smart home devices through a wireless connection. Secure smart home. control of smart home systems is available only fr
RF2JPDG3F–theft money line icon, outline symbol, vector illustration, concept sign
 vector flat cartoon character. developer detect hacking of database on the storage system server. private security firms usually provide audits every Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/vector-flat-cartoon-character-developer-detect-hacking-of-database-on-the-storage-system-server-private-security-firms-usually-provide-audits-every-image368054069.html
vector flat cartoon character. developer detect hacking of database on the storage system server. private security firms usually provide audits every Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/vector-flat-cartoon-character-developer-detect-hacking-of-database-on-the-storage-system-server-private-security-firms-usually-provide-audits-every-image368054069.htmlRF2CAP8M5–vector flat cartoon character. developer detect hacking of database on the storage system server. private security firms usually provide audits every
 Logos are vector based built in Illustrator software. It is fully editable and scanalable without losing resolution. Improve your visibility and Get a Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/logos-are-vector-based-built-in-illustrator-software-it-is-fully-editable-and-scanalable-without-losing-resolution-improve-your-visibility-and-get-a-image425864204.html
Logos are vector based built in Illustrator software. It is fully editable and scanalable without losing resolution. Improve your visibility and Get a Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/logos-are-vector-based-built-in-illustrator-software-it-is-fully-editable-and-scanalable-without-losing-resolution-improve-your-visibility-and-get-a-image425864204.htmlRF2FMRP3T–Logos are vector based built in Illustrator software. It is fully editable and scanalable without losing resolution. Improve your visibility and Get a
RF2AP7PY0–Scam types color icons set. Inheritance, home rental fraudulent scheme. Computer hacking. Employment scamming. Cybercrime. Financial scamming. Illegal
 Password phising on display laptop screen campaign for web website home homepage landing page template banner white isolated background with flat Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/password-phising-on-display-laptop-screen-campaign-for-web-website-home-homepage-landing-page-template-banner-white-isolated-background-with-flat-image383213994.html
Password phising on display laptop screen campaign for web website home homepage landing page template banner white isolated background with flat Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/password-phising-on-display-laptop-screen-campaign-for-web-website-home-homepage-landing-page-template-banner-white-isolated-background-with-flat-image383213994.htmlRF2D7CWA2–Password phising on display laptop screen campaign for web website home homepage landing page template banner white isolated background with flat
 Young man in hoodie with several laptops flat color vector faceless character. Student working at home. Remote, freelance job. Hacking. Isolated Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/young-man-in-hoodie-with-several-laptops-flat-color-vector-faceless-character-student-working-at-home-remote-freelance-job-hacking-isolated-image380455640.html
Young man in hoodie with several laptops flat color vector faceless character. Student working at home. Remote, freelance job. Hacking. Isolated Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/young-man-in-hoodie-with-several-laptops-flat-color-vector-faceless-character-student-working-at-home-remote-freelance-job-hacking-isolated-image380455640.htmlRF2D2Y71C–Young man in hoodie with several laptops flat color vector faceless character. Student working at home. Remote, freelance job. Hacking. Isolated
RF2Y1H4CY–Cyber security and artificial intelligence icons High-Quality Vector Icons Collection with Editable Stroke. Ideal for Professional and Creative Projec
 Danger to children infographics demonstrated danger of electricity lock on window run on track and hacking hackers flat compositions vector illustrati Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/danger-to-children-infographics-demonstrated-danger-of-electricity-lock-on-window-run-on-track-and-hacking-hackers-flat-compositions-vector-illustrati-image471041498.html
Danger to children infographics demonstrated danger of electricity lock on window run on track and hacking hackers flat compositions vector illustrati Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/danger-to-children-infographics-demonstrated-danger-of-electricity-lock-on-window-run-on-track-and-hacking-hackers-flat-compositions-vector-illustrati-image471041498.htmlRF2JA9P6J–Danger to children infographics demonstrated danger of electricity lock on window run on track and hacking hackers flat compositions vector illustrati
RF2PNEA74–Cyber gadgets line icons collection. Cybersecurity, Encryption, Hacking, Firewall, Malware, Phishing, Cybercrime vector and linear illustration. VPN
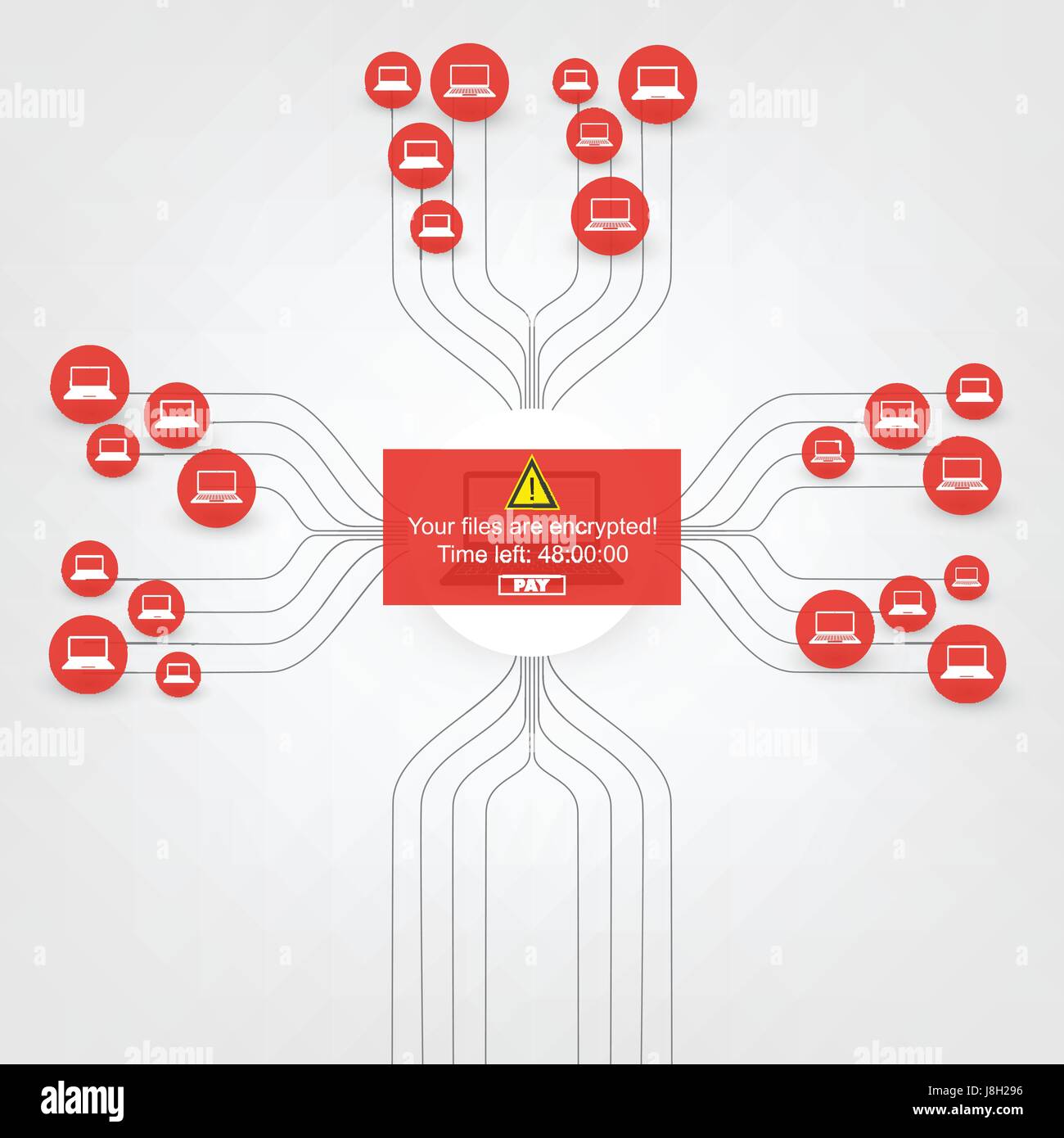
 Encrypted Files,Lost Documents,Ransomware Attack,Failed,Vulnerable Network Threat Protection - IT Security, Corporate Networking Concept Design Vector Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-encrypted-fileslost-documentsransomware-attackfailedvulnerable-network-142975146.html
Encrypted Files,Lost Documents,Ransomware Attack,Failed,Vulnerable Network Threat Protection - IT Security, Corporate Networking Concept Design Vector Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-encrypted-fileslost-documentsransomware-attackfailedvulnerable-network-142975146.htmlRFJ8H276–Encrypted Files,Lost Documents,Ransomware Attack,Failed,Vulnerable Network Threat Protection - IT Security, Corporate Networking Concept Design Vector
RF2BMJ1KM–Set of 36 UI Icons and symbols for battery, setup, clock, hacking, goal Vector Illustration
 Danger to children infographics demonstrated danger of electricity lock on window run on track and hacking hackers flat compositions vector illustrati Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/danger-to-children-infographics-demonstrated-danger-of-electricity-lock-on-window-run-on-track-and-hacking-hackers-flat-compositions-vector-illustrati-image471018384.html
Danger to children infographics demonstrated danger of electricity lock on window run on track and hacking hackers flat compositions vector illustrati Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/danger-to-children-infographics-demonstrated-danger-of-electricity-lock-on-window-run-on-track-and-hacking-hackers-flat-compositions-vector-illustrati-image471018384.htmlRF2JA8MN4–Danger to children infographics demonstrated danger of electricity lock on window run on track and hacking hackers flat compositions vector illustrati
 IOT cyber security padlock concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/iot-cyber-security-padlock-concept-personal-data-safety-internet-of-things-smart-home-cyber-attack-hacker-attack-danger-firewall-innovation-system-image240255051.html
IOT cyber security padlock concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/iot-cyber-security-padlock-concept-personal-data-safety-internet-of-things-smart-home-cyber-attack-hacker-attack-danger-firewall-innovation-system-image240255051.htmlRFRXTFNF–IOT cyber security padlock concept. Personal data safety Internet of Things smart home cyber attack. Hacker attack danger firewall innovation system
 Funny, cute, crazy cartoon thief characters. Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/funny-cute-crazy-cartoon-thief-characters-image212463077.html
Funny, cute, crazy cartoon thief characters. Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/funny-cute-crazy-cartoon-thief-characters-image212463077.htmlRFP9JER1–Funny, cute, crazy cartoon thief characters.
 Smart house IOT cybersecurity spider concept. Personal data safety Internet of Things cyber attack. Hacker attack danger firewall innovation system Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/smart-house-iot-cybersecurity-spider-concept-personal-data-safety-internet-of-things-cyber-attack-hacker-attack-danger-firewall-innovation-system-image240575398.html
Smart house IOT cybersecurity spider concept. Personal data safety Internet of Things cyber attack. Hacker attack danger firewall innovation system Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/smart-house-iot-cybersecurity-spider-concept-personal-data-safety-internet-of-things-cyber-attack-hacker-attack-danger-firewall-innovation-system-image240575398.htmlRFRYB4AE–Smart house IOT cybersecurity spider concept. Personal data safety Internet of Things cyber attack. Hacker attack danger firewall innovation system
 Robber open safe. Thief and money vault. Criminal vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/robber-open-safe-thief-and-money-vault-criminal-vector-illustration-image351658939.html
Robber open safe. Thief and money vault. Criminal vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/robber-open-safe-thief-and-money-vault-criminal-vector-illustration-image351658939.htmlRF2BC3CFR–Robber open safe. Thief and money vault. Criminal vector illustration
 Smart house IOT cybersecurity spider concept. Personal data safety Internet of Things cyber attack. Hacker attack danger firewall innovation system Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/smart-house-iot-cybersecurity-spider-concept-personal-data-safety-internet-of-things-cyber-attack-hacker-attack-danger-firewall-innovation-system-image240435562.html
Smart house IOT cybersecurity spider concept. Personal data safety Internet of Things cyber attack. Hacker attack danger firewall innovation system Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/smart-house-iot-cybersecurity-spider-concept-personal-data-safety-internet-of-things-cyber-attack-hacker-attack-danger-firewall-innovation-system-image240435562.htmlRFRY4P0A–Smart house IOT cybersecurity spider concept. Personal data safety Internet of Things cyber attack. Hacker attack danger firewall innovation system
RF2ANTPKC–Vpn icon set. Include creative elements , archiving, site security, home server, cloud storage hacking icons. Can be used for report, presentation
 Self-drawing with one line of a closed padlock on a white background. Unlock sign. Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/self-drawing-with-one-line-of-a-closed-padlock-on-a-white-background-unlock-sign-image433962480.html
Self-drawing with one line of a closed padlock on a white background. Unlock sign. Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/self-drawing-with-one-line-of-a-closed-padlock-on-a-white-background-unlock-sign-image433962480.htmlRF2G60KG0–Self-drawing with one line of a closed padlock on a white background. Unlock sign.
RF2AB5CDM–Vpn icon set. Include creative elements , archiving, site security, home server, cloud storage hacking icons. Can be used for report, presentation
 Vector illustration concept. people are holding key to trying to enter and unlock application security but fail because executive protection and produ Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/vector-illustration-concept-people-are-holding-key-to-trying-to-enter-and-unlock-application-security-but-fail-because-executive-protection-and-produ-image368053951.html
Vector illustration concept. people are holding key to trying to enter and unlock application security but fail because executive protection and produ Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/vector-illustration-concept-people-are-holding-key-to-trying-to-enter-and-unlock-application-security-but-fail-because-executive-protection-and-produ-image368053951.htmlRF2CAP8FY–Vector illustration concept. people are holding key to trying to enter and unlock application security but fail because executive protection and produ
 Logos are vector based built in Illustrator software. It is fully editable and scalable without losing resolution. Improve your visibility and Get a p Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/logos-are-vector-based-built-in-illustrator-software-it-is-fully-editable-and-scalable-without-losing-resolution-improve-your-visibility-and-get-a-p-image425863618.html
Logos are vector based built in Illustrator software. It is fully editable and scalable without losing resolution. Improve your visibility and Get a p Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/logos-are-vector-based-built-in-illustrator-software-it-is-fully-editable-and-scalable-without-losing-resolution-improve-your-visibility-and-get-a-p-image425863618.htmlRF2FMRNAX–Logos are vector based built in Illustrator software. It is fully editable and scalable without losing resolution. Improve your visibility and Get a p
RF2AP81MF–Scam types glyph icons set. Inheritance, home rental fraudulent scheme. Computer hacking. Employment scamming. Cybercrime. Financial scamming. Silhoue
 email camera surveillance design vector illustration eps 10 Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-email-camera-surveillance-design-vector-illustration-eps-10-126317258.html
email camera surveillance design vector illustration eps 10 Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-email-camera-surveillance-design-vector-illustration-eps-10-126317258.htmlRFH9E6XJ–email camera surveillance design vector illustration eps 10
 Security services flyers flat vector templates set. Home protection. Cyber safety. Printable leaflet design layout. Advertising web vertical banner Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/security-services-flyers-flat-vector-templates-set-home-protection-cyber-safety-printable-leaflet-design-layout-advertising-web-vertical-banner-image380472733.html
Security services flyers flat vector templates set. Home protection. Cyber safety. Printable leaflet design layout. Advertising web vertical banner Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/security-services-flyers-flat-vector-templates-set-home-protection-cyber-safety-printable-leaflet-design-layout-advertising-web-vertical-banner-image380472733.htmlRF2D300RW–Security services flyers flat vector templates set. Home protection. Cyber safety. Printable leaflet design layout. Advertising web vertical banner
 Green lock illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/green-lock-illustration-image559382589.html
Green lock illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/green-lock-illustration-image559382589.htmlRF2RE225H–Green lock illustration
 Workplace with human hands front view. Laptop with blank screen. Man work on computer. Flat vector illustration template in a trendy flat style. Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/workplace-with-human-hands-front-view-laptop-with-blank-screen-man-work-on-computer-flat-vector-illustration-template-in-a-trendy-flat-style-image570945355.html
Workplace with human hands front view. Laptop with blank screen. Man work on computer. Flat vector illustration template in a trendy flat style. Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/workplace-with-human-hands-front-view-laptop-with-blank-screen-man-work-on-computer-flat-vector-illustration-template-in-a-trendy-flat-style-image570945355.htmlRF2T4TPHF–Workplace with human hands front view. Laptop with blank screen. Man work on computer. Flat vector illustration template in a trendy flat style.
 a scam call on a smartphone. cheating on the phone. flat vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/a-scam-call-on-a-smartphone-cheating-on-the-phone-flat-vector-illustration-image461319731.html
a scam call on a smartphone. cheating on the phone. flat vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/a-scam-call-on-a-smartphone-cheating-on-the-phone-flat-vector-illustration-image461319731.htmlRF2HPEX0K–a scam call on a smartphone. cheating on the phone. flat vector illustration
 Successfully Detected and Stopped Malware or Ransomware Attack - Network Threat Protection, IT Security Concept Design, Vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-successfully-detected-and-stopped-malware-or-ransomware-attack-network-142975430.html
Successfully Detected and Stopped Malware or Ransomware Attack - Network Threat Protection, IT Security Concept Design, Vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-successfully-detected-and-stopped-malware-or-ransomware-attack-network-142975430.htmlRFJ8H2HA–Successfully Detected and Stopped Malware or Ransomware Attack - Network Threat Protection, IT Security Concept Design, Vector illustration
RF2BMJHYR–Set of 9 UI Icons and symbols for dog food, bone, shorts, medical, chat Vector Illustration
 Darkweb at laptop vector linear Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/darkweb-at-laptop-vector-linear-image602807779.html
Darkweb at laptop vector linear Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/darkweb-at-laptop-vector-linear-image602807779.htmlRF2X0M7D7–Darkweb at laptop vector linear
RF2PNGT8D–Communication technology line icons collection. Internet, WiFi, Smartph, Bluetooth, Satellite, Robocall, Streaming vector and linear illustration
RF2PNWE5Y–Technology linear icons set. Smartph, Tablet, Laptop, Cybersecurity, Artificial Intelligence, Automation, Cloud line vector and concept signs
 The masked thief steals the key. Fraudster pulls in data. Stealing passwords. Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/the-masked-thief-steals-the-key-fraudster-pulls-in-data-stealing-passwords-image452242036.html
The masked thief steals the key. Fraudster pulls in data. Stealing passwords. Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/the-masked-thief-steals-the-key-fraudster-pulls-in-data-stealing-passwords-image452242036.htmlRF2H7NB98–The masked thief steals the key. Fraudster pulls in data. Stealing passwords.
 Robber open safe. Thief and money vault. Criminal vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/robber-open-safe-thief-and-money-vault-criminal-vector-illustration-image351660405.html
Robber open safe. Thief and money vault. Criminal vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/robber-open-safe-thief-and-money-vault-criminal-vector-illustration-image351660405.htmlRF2BC3EC5–Robber open safe. Thief and money vault. Criminal vector illustration
RF2C90JH8–Nomadic icon vector, filled flat sign, solid pictogram isolated on white, logo illustration. Nomadic icon for presentation.
 Wireless router being secured with a padlock, symbolizing network security and data protection Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/wireless-router-being-secured-with-a-padlock-symbolizing-network-security-and-data-protection-image611883128.html
Wireless router being secured with a padlock, symbolizing network security and data protection Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/wireless-router-being-secured-with-a-padlock-symbolizing-network-security-and-data-protection-image611883128.htmlRF2XFDK4T–Wireless router being secured with a padlock, symbolizing network security and data protection
 Self-drawing with one line of a closed padlock on a white background. Unlock sign. Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/self-drawing-with-one-line-of-a-closed-padlock-on-a-white-background-unlock-sign-image432083713.html
Self-drawing with one line of a closed padlock on a white background. Unlock sign. Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/self-drawing-with-one-line-of-a-closed-padlock-on-a-white-background-unlock-sign-image432083713.htmlRF2G2Y355–Self-drawing with one line of a closed padlock on a white background. Unlock sign.
RF2AWWKGB–Vpn icon set. Include creative elements , archiving, site security, home server, cloud storage hacking icons. Can be used for report, presentation
RF2CCM0NP–Email-19 Special lineal color icon. Illustration symbol design template for web mobile UI element. Perfect color modern pictogram on editable stroke.
RF2AXM2WW–Hacking car icon vector. Isolated contour symbol illustration
RF2AP80CE–Scam types chalk icons set. Inheritance, home rental fraudulent scheme. Computer hacking. Employment scamming. Financial scamming. Illegal money gain.
 email camera surveillance design vector illustration eps 10 Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-email-camera-surveillance-design-vector-illustration-eps-10-126316824.html
email camera surveillance design vector illustration eps 10 Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-email-camera-surveillance-design-vector-illustration-eps-10-126316824.htmlRFH9E6B4–email camera surveillance design vector illustration eps 10
 Two computer monitors with large cracks in the screens, representing hardware failure Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/two-computer-monitors-with-large-cracks-in-the-screens-representing-hardware-failure-image612554634.html
Two computer monitors with large cracks in the screens, representing hardware failure Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/two-computer-monitors-with-large-cracks-in-the-screens-representing-hardware-failure-image612554634.htmlRF2XGG7K6–Two computer monitors with large cracks in the screens, representing hardware failure
 Mechanic golden lock illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/mechanic-golden-lock-illustration-image559381974.html
Mechanic golden lock illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/mechanic-golden-lock-illustration-image559381974.htmlRF2RE21BJ–Mechanic golden lock illustration
 Workplace with human hands front view. Laptop with blank screen. Man work on computer. Flat vector illustration template in a trendy flat style. Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/workplace-with-human-hands-front-view-laptop-with-blank-screen-man-work-on-computer-flat-vector-illustration-template-in-a-trendy-flat-style-image570539797.html
Workplace with human hands front view. Laptop with blank screen. Man work on computer. Flat vector illustration template in a trendy flat style. Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/workplace-with-human-hands-front-view-laptop-with-blank-screen-man-work-on-computer-flat-vector-illustration-template-in-a-trendy-flat-style-image570539797.htmlRF2T46999–Workplace with human hands front view. Laptop with blank screen. Man work on computer. Flat vector illustration template in a trendy flat style.
 a scam call on a smartphone. cheating on the phone. flat vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/a-scam-call-on-a-smartphone-cheating-on-the-phone-flat-vector-illustration-image367755553.html
a scam call on a smartphone. cheating on the phone. flat vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/a-scam-call-on-a-smartphone-cheating-on-the-phone-flat-vector-illustration-image367755553.htmlRF2CA8KXW–a scam call on a smartphone. cheating on the phone. flat vector illustration
 Successfully Detected and Stopped Malware or Ransomware Attack - Network Threat Protection, IT Security Concept Design, Vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-successfully-detected-and-stopped-malware-or-ransomware-attack-network-142975523.html
Successfully Detected and Stopped Malware or Ransomware Attack - Network Threat Protection, IT Security Concept Design, Vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-successfully-detected-and-stopped-malware-or-ransomware-attack-network-142975523.htmlRFJ8H2MK–Successfully Detected and Stopped Malware or Ransomware Attack - Network Threat Protection, IT Security Concept Design, Vector illustration
RF2BMJHYD–Set of 9 UI Icons and symbols for dog food, bone, shorts, medical, chat Vector Illustration
RF2DMT297–Key password man icon. Isometric of key password man vector icon for web design isolated on white background
RF2PNXHHK–Technological aptitude line icons collection. Innovation, Digital, Coding, Robotics, Cybersecurity, Programming, Automation vector and linear
RF2PNX6YK–Technology linear icons set. Smartph, Tablet, Laptop, Cybersecurity, Artificial Intelligence, Automation, Cloud line vector and concept signs
 Robber open safe. Thief and money vault. Criminal vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/robber-open-safe-thief-and-money-vault-criminal-vector-illustration-image351657596.html
Robber open safe. Thief and money vault. Criminal vector illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/robber-open-safe-thief-and-money-vault-criminal-vector-illustration-image351657596.htmlRF2BC3ART–Robber open safe. Thief and money vault. Criminal vector illustration
 Grandmother hacker sits on an armchair with laptop and cat. grandma is thief programmer. internet Computer security. Old woman and PC Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-grandmother-hacker-sits-on-an-armchair-with-laptop-and-cat-grandma-145180058.html
Grandmother hacker sits on an armchair with laptop and cat. grandma is thief programmer. internet Computer security. Old woman and PC Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-grandmother-hacker-sits-on-an-armchair-with-laptop-and-cat-grandma-145180058.htmlRFJC5EJ2–Grandmother hacker sits on an armchair with laptop and cat. grandma is thief programmer. internet Computer security. Old woman and PC
 Self-drawing with one line of a closed padlock on a white background. Unlock sign. Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/self-drawing-with-one-line-of-a-closed-padlock-on-a-white-background-unlock-sign-image425537586.html
Self-drawing with one line of a closed padlock on a white background. Unlock sign. Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/self-drawing-with-one-line-of-a-closed-padlock-on-a-white-background-unlock-sign-image425537586.htmlRF2FM8WEX–Self-drawing with one line of a closed padlock on a white background. Unlock sign.
RF2AA4P32–Vpn icon set. Include creative elements , archiving, site security, home server, cloud storage hacking icons. Can be used for report, presentation
RF2D9WGFP–Modern hacker icon, flat style
RF2AXJCH2–Hacking car icon vector. Isolated contour symbol illustration
RF2ARG1T5–Scam types drop shadow black glyph icons set. Inheritance, home rental fraudulent scheme. Computer hacking. Employment scamming. Financial scamming. I
 Golden lock illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/golden-lock-illustration-image559383695.html
Golden lock illustration Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/golden-lock-illustration-image559383695.htmlRF2RE23H3–Golden lock illustration
 Workplace with human hands front view. Laptop with blank screen. Man work on computer. Flat vector illustration template in a trendy flat style. Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/workplace-with-human-hands-front-view-laptop-with-blank-screen-man-work-on-computer-flat-vector-illustration-template-in-a-trendy-flat-style-image570357798.html
Workplace with human hands front view. Laptop with blank screen. Man work on computer. Flat vector illustration template in a trendy flat style. Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/workplace-with-human-hands-front-view-laptop-with-blank-screen-man-work-on-computer-flat-vector-illustration-template-in-a-trendy-flat-style-image570357798.htmlRF2T3X15A–Workplace with human hands front view. Laptop with blank screen. Man work on computer. Flat vector illustration template in a trendy flat style.
 Encrypted Files,Lost Documents,Ransomware Attack,Failed,Vulnerable Network Threat Protection - IT Security, Corporate Networking Concept Design Vector Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-encrypted-fileslost-documentsransomware-attackfailedvulnerable-network-142975202.html
Encrypted Files,Lost Documents,Ransomware Attack,Failed,Vulnerable Network Threat Protection - IT Security, Corporate Networking Concept Design Vector Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-encrypted-fileslost-documentsransomware-attackfailedvulnerable-network-142975202.htmlRFJ8H296–Encrypted Files,Lost Documents,Ransomware Attack,Failed,Vulnerable Network Threat Protection - IT Security, Corporate Networking Concept Design Vector
RF2BMCW4T–Stock Vector Icon Set of 16 Line Symbols for stationary, paper pin, fragrance, sms, chat Vector Illustration
RF2PNE7M3–Tech industry line icons collection. Innovation, Disruption, Blockchain, Cybersecurity, Cloud, AI, Robotics vector and linear illustration. Automation
RF2PNWMF8–Information devices linear icons set. Tablet, Smartph, Laptop, Desktop, Smartwatch, E-reader, Wearables line vector and concept signs. Phablet,Router
 Grandmother hacker sits on an armchair with laptop and cat. grandma is thief programmer. internet Computer security. Old woman and PC Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-grandmother-hacker-sits-on-an-armchair-with-laptop-and-cat-grandma-145179880.html
Grandmother hacker sits on an armchair with laptop and cat. grandma is thief programmer. internet Computer security. Old woman and PC Stock Vectorhttps://www.alamy.com/image-license-details/?v=1https://www.alamy.com/stock-photo-grandmother-hacker-sits-on-an-armchair-with-laptop-and-cat-grandma-145179880.htmlRFJC5EBM–Grandmother hacker sits on an armchair with laptop and cat. grandma is thief programmer. internet Computer security. Old woman and PC